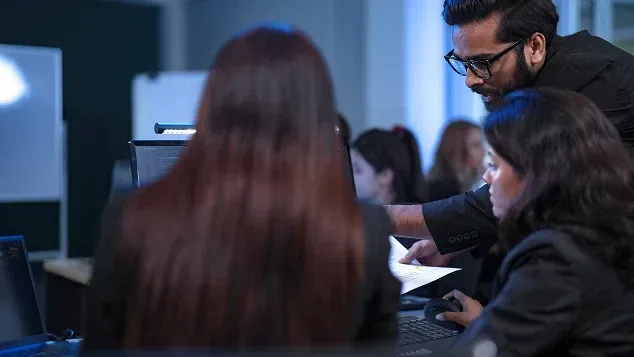
Key Features of Our Security Operations Center (SOC)
Advanced Security at Your Fingertips

Continuous surveillance to detect and mitigate threats.
Rapid identification and mitigation of security incidents.
Stay ahead with insights into the latest global security threats.

Centralised log management for analysis and threat correlation.
AI-powered tools to detect hidden threats proactively.
Ensure adherence to regulations like GDPR, ISO 27001, and more.
Regular scans to identify and remediate security gaps.
Detailed RCA investigation of security incidents.
Secure on-premises and cloud environments.

Visibility into security posture with actionable insights.
See all Features & Benefits
Download BrochureKey Benefits of Our SOC Solutions
Proactive Defense for a Secure Business Future
Reduced Risk Exposure
Minimise the likelihood of data breaches and cyberattacks.

Rapid Incident Response
Quick containment and mitigation of security threats.
Cost Efficiency
Lower costs by outsourcing to a professional SOC.

Enhanced Compliance
Continuous monitoring to meet regulatory requirements.
Improved Threat Visibility
Centralised view of security events across the organization.

Operational Resilience
Proactive threat management to strengthen business continuity.

Expert Security Support
24/7 access to certified cybersecurity professionals.

Data Protection
Advanced encryption and monitoring to secure data.
Our Clients
From driving renewed value to embracing new technologies, we help our clients accelerate digital transformation and promote growth

Ready to Strengthen Your Security with SOC Solutions?
Share your details and we’ll get you connected.
Got Questions?
Find your answers right here.
Explore Related Security Solutions
Discover other Tata Tele Business Services products that complement our SOC offerings.
Please Fill in Your Details and We'll Call You Back!
Connect With Us
Please Fill in Your Details and We'll Call You Back!
Please Fill in Your Details and We'll Call You Back!